Cloud infrastructure
Accreditation boundary, SSP, continuous monitoring, FedRAMP Moderate inheritance where applicable.
AWS GovCloud · Terraform
by with
vallark (n.) — from vallum 'palisaded rampart' + ark 'vessel': a defensive perimeter that arrives ready to hold.
For .mil mobile program offices
A .mil mobile ATO typically takes 12+ months of compliance plumbing before anyone writes a feature. Vallark is SigilArk's delivery capability that ships that floor pre-built — controls, documentation, and automated gates across every layer your program has to authorize.
Engage SigilArk →I · Scope
Every .mil mobile program has to authorize a full stack, not just the app. Each layer meets RMF independently and ships its own evidence package.
Accreditation boundary, SSP, continuous monitoring, FedRAMP Moderate inheritance where applicable.
AWS GovCloud · Terraform
DISA SRG + STIG coverage, SBOM, SLSA provenance, every endpoint audited, CUI classification enforced, audit trail tied to identity.
Hono.js on AWS Lambda · API Gateway
FIPS 140-3 crypto, strict CSP, no client-side CUI, Section 508 / WCAG AA, VPAT, sessions bound to CAC-backed identity.
React · BFF pattern · CloudFront edge
DISA Mobile SRG, App Attest, certificate pinning, root / debugger detection, keyboard and screenshot discipline, release-build log stripping.
Swift · iOS 16+
DISA Mobile SRG, Play Integrity, certificate pinning, root / debugger detection, keyboard and screenshot discipline, release-build log stripping.
Kotlin · Android 13+
And the platforms aren't symmetric. iOS has no public API to prevent screenshots, so where Android writes a prevention control, iOS writes a compensating detection-and-audit control — and both rows have to be documented, tested, and defensible before one STIG control is closed.
Every layer also ships in STIG-hardened RHEL-9 UBI containers — refreshed nightly to maintain a clean 0 / 0 / 0 / 0 CVE scan, every day, across every program.
Built on
II · The marathon
The work is genuinely that big. The rigor is warranted — mobile is the highest-risk category, and every friction point below exists for a reason. The question isn't whether to clear them; it's whether each program clears them from scratch.
Mobile is the risk category cyber leadership worries about most. Every control needs evidence. Every exception needs a signed compensating-control row. Every platform gap gets questioned.
iOS can't prevent screenshots. Android can. The same STIG row is a prevention on one platform and a compensating control on the other — both built, tested, defended. Every divergent surface doubles the matrix.
SSP. POA&M. VPAT. FIPS 140-3 validation. DISA Mobile STIG checklist. App-revocation runbook. Threat model. Data inventory. CUI acknowledgment. Version-controlled to the code that implements them.
Run two .mil mobile programs and you're copy-pasting controls across codebases. Every iOS privacy change or CVE means every fork needs the patch, the re-test, the evidence update. By program three, maintenance exceeds delivery.
III · The relief
SigilArk brings Vallark to every .mil mobile engagement as five pre-built, ATO-ready starter projects. Your developers clone them on day one and begin building features inside a scaffold that is already compliant.
One per target — infrastructure, API, web console, iOS, Android. Each ships with STIG / RMF controls implemented and evidence generated. Your developers clone and begin writing features inside an ATO-compliant scaffold.
SSP shell. STIG checklists. Compensating-control inventory. Threat model. Data inventory. VPAT baseline. Pre-filled to the level Vallark is implemented at. Your team adds the program-specific rows, not the framework.
CI runs the 22 + 8 control matrix on every PR. Fails on drift. Blocks release on missing evidence. Produces the evidence bundle your ISSO reviews — the same green gate your engineers see.
One baseline, updated in one place when OS APIs shift or a CVE lands. The patch lands once and propagates to every program in your portfolio — the floor stays current, without drifting copy-paste forks.
The compliance floor stops being the critical path.
Your program's first release
Month 12 → Week 4
Typical .mil mobile program
With Vallark
IV · On the device
Every Vallark control lands as actual UI on real iOS and Android devices. Here's what four of them look like in flight.
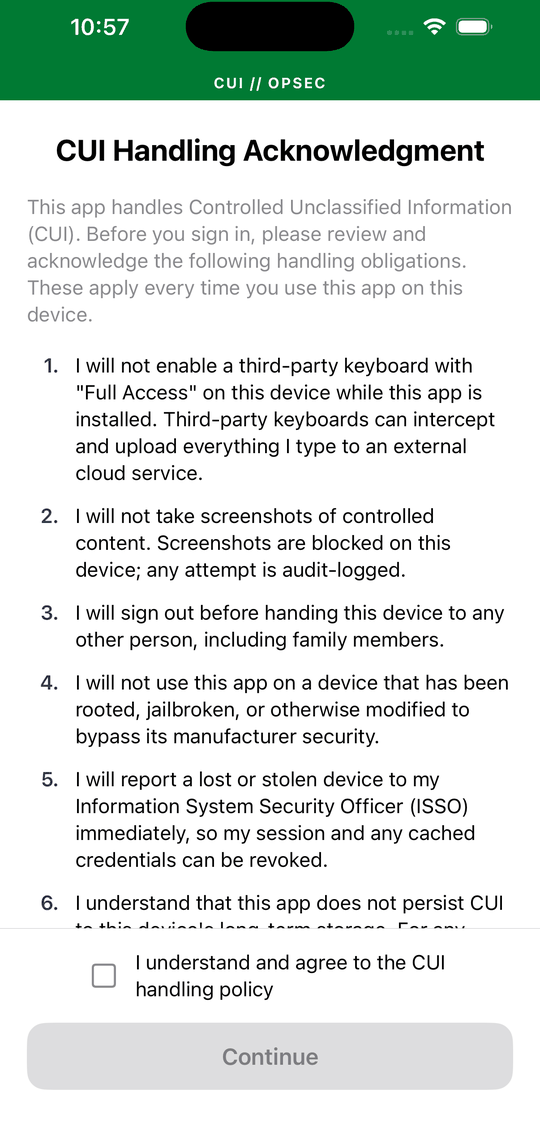
Classification banner pinned to every authenticated view, including first-launch. The CUI acknowledgment gate runs underneath — versioned, so policy changes re-prompt.
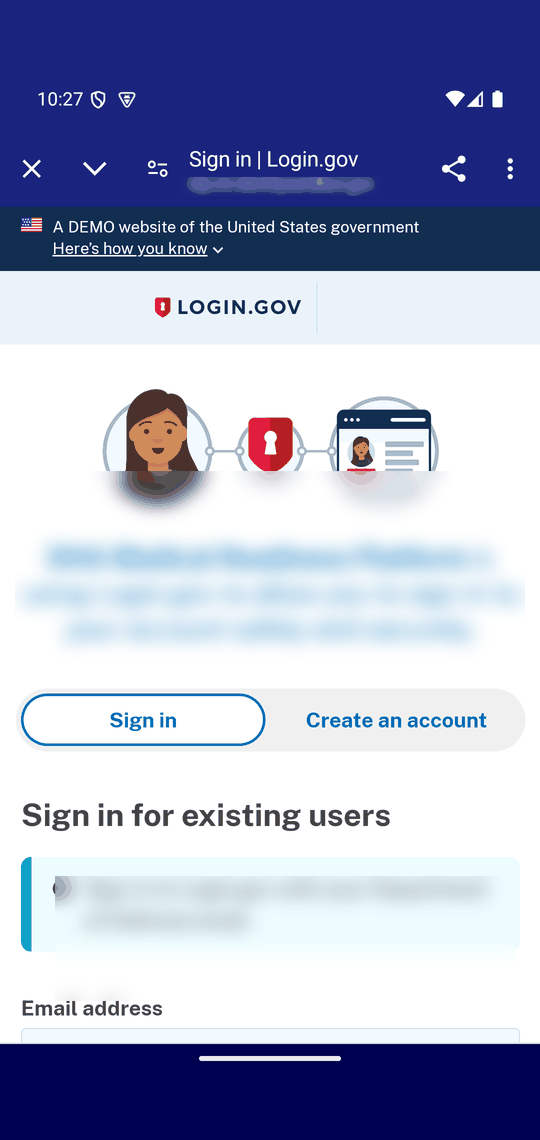
Sign-in opens the IdP in-app. Same flow for AWS Cognito, Okta, MyAuth, or any OIDC provider — the surrounding chrome doesn't change.
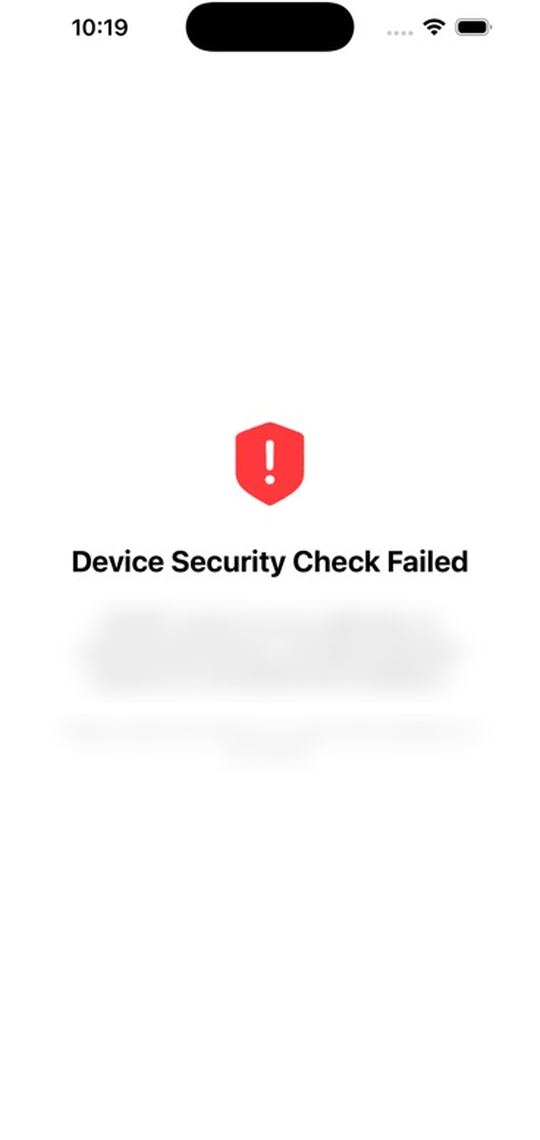
Launch refuses on devices showing signs of root or jailbreak. The deny screen names the cause so the user knows what's wrong.
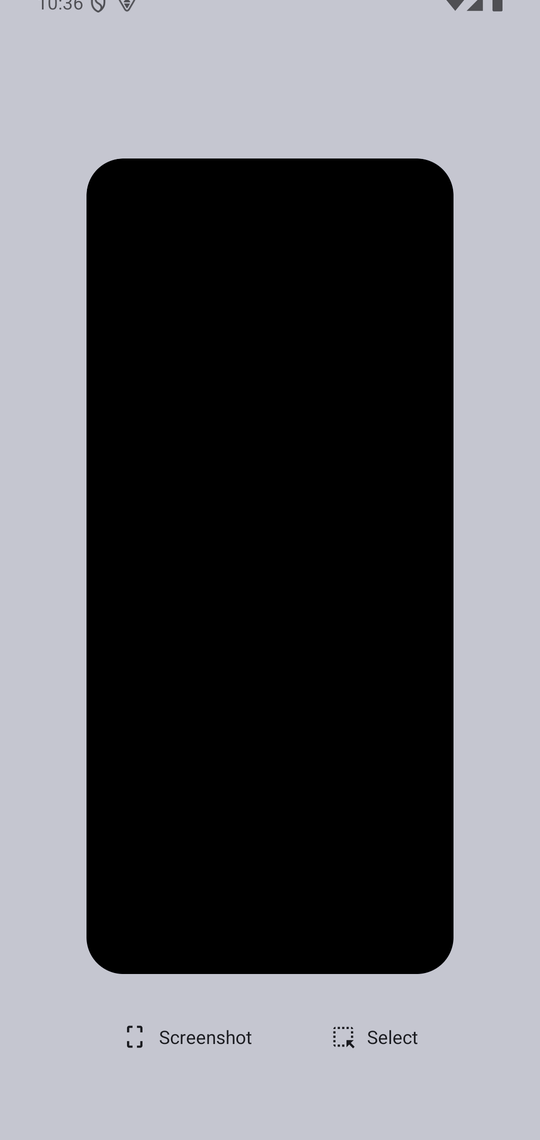
Backgrounded app shows a privacy screen instead of the active view. Prevents shoulder-surfing in the app-switcher carousel.
V · Identity
CAC on web. Modern IdPs across every surface. JWT / OIDC orchestration in the API. PKCE on mobile. The hardest gate in a .mil program ships pre-wired, not bolted on.
PIV smart-card auth lands in the web starter on day one — the credential most program offices ask about first. Cert chain validation, OCSP, and the middle-tier bridge to the API ship pre-wired in the starter.
Pick your IdP per program; the surrounding flow stays uniform across surfaces. Any OIDC / PKCE provider drops in via standard configuration — the named providers below are pre-wired in the starter.
The API starter handles the full JWT / OIDC authn and authz flow end-to-end. Web, mobile, and third-party API clients all flow through the same identity contract — one code path to audit, one place to govern.
Mobile auth has its own constraints — no client secret, redirect handling, attestation binding. The mobile starter ships PKCE wired through the trust broker so the flow is uniform across iOS and Android.
Identity providers, supported out of the box
VI · Proven in production
Two .mil deployments running on the Vallark floor today — IL4 and IL5 GovCloud, both maintained continuously since launch.
Multiplayer iOS, Android, and web clients coordinated over real-time WebSocket. In-game interrupts, gameplay replays, and after-action review across concurrent mission scenarios. Hono.js API on AWS Lambda; Postgres for state.
iOS and Android provider apps with offline mission editing and deferred sync. Drag-and-drop editor pushes updates to every device. Command-level console with readiness dashboards — serving military, international, and disaster-relief engagements. Hono.js on AWS Lambda; Postgres for state.
~5K
Daily active users
6 mo
Continuous production
IL4 + IL5
GovCloud accreditation
Continuous ATOs held. Nightly CVE / STIG / Trivy scans auto-resolve via Glyphon-managed UBI 9 containers. Both deployments meet the full 22 + 8 mobile STIG + compensating-control matrix out of the box.
VII · The control set
Every control in the floor, mapped to its citation.
The 22 + 8 matrix — proven in prior .mil deployments — extends the native-mobile control set across the web console and the API surface, so mobile controls are load-bearing end-to-end. Each control below maps to the authoritative DoD or NIST publication that defines it.
Coverage at a glance
30 controls × 4 platforms. 103 cells apply — the rest are platform-asymmetric by design.
Full-parity controls · 22
Controls that ship with matching implementations across native mobile clients, the web console, and the API reference.
Reject launch on devices with signs of root or jailbreak. Platform-specific heuristics on native clients.
Detect attached debuggers at launch and prevent debugger attachment on release builds.
Hardware-backed attestation via Play Integrity (Android) and App Attest (iOS); server verifies the token before trusting the client.
Every authenticated mobile request carries X-Attestation-Token; omitted from web requests by design under the BFF model.
Classification banner visible on every authenticated view; banner text configurable to the marking your program requires.
Static source-walk in CI asserts every screen renders the banner. Prevents silent drift on new routes.
Autocorrect, predictive text, personalized-learning, and autofill suppressed on fields handling CUI.
First-launch modal reminds users of CUI handling obligations. Versioned so policy changes re-prompt.
Fixed precedence: jailbreak → CUI ack → auth → upgrade check → attestation → app. Compiled-in; no runtime toggles.
App tokens wiped 120 seconds after backgrounding. Cold start forces OIDC re-authentication.
Refresh and access tokens never touch disk — no Keychain, no SharedPreferences, no localStorage.
Release builds pin the API TLS certificate; backup pin enables rotation overlap; pin failure is a hard error.
Compensating on web — browser CA store + HSTS + CT logs per standard web posture.
HTTP disk cache off by default; CUI responses additionally tagged Cache-Control: no-store.
Every client and the API gateway enforce a 30-second cap. No unbounded waits on any path.
Every authenticated request carries X-App-Version and X-Platform-Version. Server audit-logs both and enforces a minimum-version floor.
Authorization: Bearer <jwt> added server-side by the BFF for web, client-side for mobile. Validated at the API on every route.
Server returns 426 when X-App-Version is below floor. Client shows a non-dismissable update prompt.
Client intercepts 403 + RFC 7807 code=attestation_failed, triggers a re-attestation flow rather than crashing.
CI fails if any code path writes to disk outside an explicit allowlist. Catches persistence regressions before they ship.
CI verifies all required middleware and client interceptors are registered in the correct order.
Single provider-agnostic codepath with quirk flags isolating Login.gov, MyAuth, Okta, Azure AD, Cognito, Keycloak differences.
Platform-specific controls · 8
Controls where the ideal implementation differs per target, or where one platform's API surface forces a compensating posture.
Android blocks screenshot capture at the platform window level. iOS and web detect the event and audit it — those platforms do not expose a prevention API.
Compensating on iOS (detect-only) and web (detect-only via visibilitychange).
Thumbnail obscured when the app is backgrounded. Secure-window flag on Android, material blur overlay on iOS.
Android suppresses the text-toolbar copy/cut items. Web blocks copy and cut events on CUI inputs. iOS is best-effort with no public API.
Compensating on iOS — no public SwiftUI API to suppress text-toolbar items.
Android calls ClipboardManager.clearPrimaryClip() on sign-out and background transitions.
Compensating on iOS — no public API to clear the system clipboard from an app.
Release builds strip debug logs: R8 -assumenosideeffects on Android, os.Logger scoping on iOS, Vite in web production, Pino log-level pinned on API.
Per-platform lint rules (detekt-no-cui-in-log, swiftlint-no-cui-in-log, eslint-no-cui-in-log) plus source-walk tests catch CUI leaking into logs.
Hardware-backed attestation via Google Play Integrity API. Server verifies verdict, nonce, and device-integrity fields on every attested request.
Hardware-backed attestation via Apple App Attest. Server verifies assertion against the registered key store.
For a SigilArk-led .mil mobile engagement, this matrix lands on day one.
by with